According to a recent Twitter announcement from Elon Musk, buyers in the United States can now purchase a Tesla vehicle...
Tesla

Tesla Motors is an American automobile company founded in 2003 that produces electric vehicles. Based on 2019 sales, Tesla ranked as the world’s best-selling battery electric passenger car manufacturer.
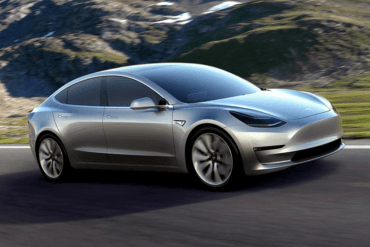
Tesla’s Model 3 ranks as the world’s best-selling plug-in electric vehicle as of March 2020. Even though the company has never recorded a profitable year, they have had several profitable quarters throughout their history.
In addition to its Model S and Model 3 electric cars, they have the Model X SUV and Model Y CUV (get it, models S, 3, X, and Y?)
Tesla is also working on the Tesla Semi, an all-electric Class 8 semi-trailer truck that comes in two variants: one with a 300-mile range and the other with a 500-mile range. The trucks are scheduled to be available in 2021
Tesla also has plans for a Cybertruck, which will have an expected range of 500 miles. The Cybertruck is also expected in 2021.
Well lah-dee-dah, the refresh of Tesla’s Model S is here. I’d like to sound more impressed, but Elon has been...
The Tesla Model 3 and Hyundai Kona Electric are completely different, but both are trying to knock down the barriers...
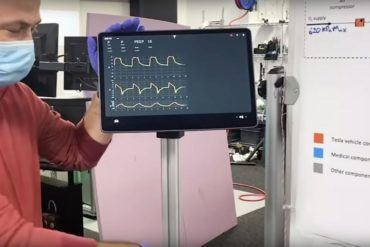
As Coronavirus cases continue to spike, Tesla is building a ventilator based on their vehicle parts. This video from Tesla...
The Tesla Model S has the looks of a luxury car, the stance of a sports sedan, and the performance...
“So many memes, so little time,” said the internet when Tesla launched the Cybertruck. The post-apocalyptic-looking machine will be Tesla’s...
There’s no doubt, the Tesla Cybertruck is one of the more polarizing concepts to come out of the automotive industry...
The Tesla Cybertruck is the automaker’s first pickup. Three different trim levels and powertrains are on offer. It has a...
The Tesla Model 3 and Hyundai Kona Electric are two radically different animals. However, both are trying to knock down the...
The base Tesla Model 3 starts at $35,000 and has a range of over 200 miles. Tesla is looking to...
Polestar will reveal their next model at the Geneva International Motor Show. The Polestar 2 will compete with other high...
The Audi e-tron GT concept is Audi’s vision for a fast EV. However, the Tesla Model S lords over many...
The Future In Front of Me, The Past Behind Me is a gasoline-fueled narrative by automotive journalist Tony Borroz. It...
Last Wednesday night Tesla made an announcement. Many of us waited with baited breath to discover what was up their...
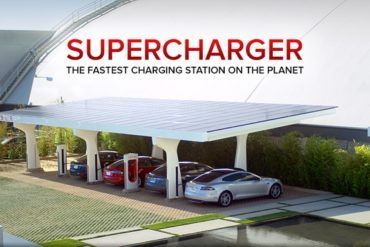
Tesla Motors CEO Elon Musk, in a recent phone conference, announced that all Tesla vehicles will now be equipped with the...
Tesla announced this week they will begin producing a new version of the Model S and Model X, the P100D....
In the discussions surrounding autonomous vehicles, safety is often the first concern. Invariably, the concern is that self-driving cars would...
During Tesla’s quarterly shareholder’s meeting, Elon Musk admitted to making mistakes but brazenly indicated that an overhauling was coming. This is...
The much anticipated Tesla Model 3 was revealed tonight in a relatively short presentation. It was much anticipated because people...
This is a guest post by IG and provides a financial analysis of Tesla Motors. All opinions are those of...
Leading up to Tesla Motors‘ “D” announcement, the press, fans, and Elon Musk’s critics could not stop speculating about what...
Thanks the US government mandate that automotive fleets reach 54.5 mpg by 2025, the dawn of the hybrid supercar is...
There’s no doubt that Tesla Motors has been kicking ass recently. Despite popular pundits constantly trying to find something wrong...
Well, you’re probably all too drunk to be reading this, but maybe you’ll catch it in the morning. As you...
Tesla Chief Executive Officer Elon Musk has to be feeling pretty good about now. Arch rival Fisker Automotive has seen...
It isn’t often that I use the basis of an article to promote the work of another automotive publication. While...
The driving and overall ownership experience of an electric vehicle is far different than that of an internal combustion engine....
Lawsuits are in the air. The latest comes a new one aimed at Tesla Motors. Tesla is a product of...
So far Tesla Motors has defied the odds, which are stacked against any new entries in the automotive space. Last...
At current time of writing, the 2013 Tesla Model S is scheduled to launch in just 2 days and 5...